Enabling Real-time Replication for Amazon Elastic Compute Cloud (Amazon EC2)
How to enable real-time Amazon EC2 replication with Arpio and AWS Elastic Disaster Recovery
When configuring Arpio to create recovery points for your application, you have the option of enabling a recovery point objective (RPO) of "Real-time replication".
When real-time replication is enabled for an application, all Amazon EC2 instances in that application will have a near real-time recovery point objective of seconds. Arpio achieves this by leveraging an integration with AWS's Elastic Disaster Recovery Service (DRS). This article will walk through how to set up real time data replication with Arpio and DRS.
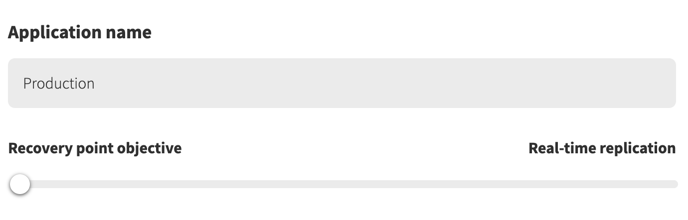
Setting your real-time recovery point
To enable real-time replication, you will need to configure your application resources in Arpio, as well as in the DRS console in your AWS account. We recommend you begin the process by configuring your applications in Arpio.
To set up real-time replication with Arpio:
- Begin the normal application creation process in the Arpio console
- When prompted to enter the details about your new application, set the Recovery point objective slider all the way to the left, to read Real-time replication.
3. In the resource selection step of the application creation flow, choose the EC2 instances you would like to protect with real-time replication.
Note: If there are some EC2 instances in this application that you would prefer to protect using snapshot replication, rather than real-time replication, you can also select those at this time.
4. Click Finish to complete your application creation and prompt Arpio to begin backing up your application for the first time.
Arpio application replication and the AWS Replication Agent
After Arpio has completed its initial back up of your new application, it will display an issue noting that real-time replication has not yet been enabled for each server in your application that is missing the AWS Replication Agent needed for DRS support. During this interim period, Arpio will default to snapshot replication.
.png?width=688&name=image%20(4).png)
To complete the set-up process for real-time replication, follow the AWS installation guide to install the AWS Replication Agent on each source server you would like Arpio to manage in your recovery environment with real-time replication.
Once you have completed the installation of the AWS Replication Agent on each relevant EC2 instance, the related issue will disappear from your console.
Note: The Amazon Elastic Disaster Recovery Service is not yet available in all AWS Regions. Please ensure that your primary and recovery regions are supported by DRS prior to enabling real-time replication on your Arpio applications. More documentation on supported regions can be found here.
Real-time replication settings
Arpio will create and manage the resources necessary for your staging environment. These resources include the subnet within which the Replication Server will be launched and the security groups that allow DRS to communicate with the Replication Agent.
If you have existing replication settings, Arpio checks them for compatibility and makes any adjustments, if needed.
If you wish to set up your own replication for staging please refer to Amazon’s official documentation for your staging area subnet and security groups.
Using both Real-time replication and snapshots in your Arpio application
If you would like to revert to using snapshots rather than real-time replication on an EC2 instance in your application, complete steps 1-4 in the Arpio set up guide above. This will generate an issue for every source server that does not have the AWS Replication Agent installed.
For the source servers that you would like Arpio to replicate using snapshots, do not install the AWS Replication Agent. Instead, follow the link in the Arpio issue to opt in to Snapshot replication.
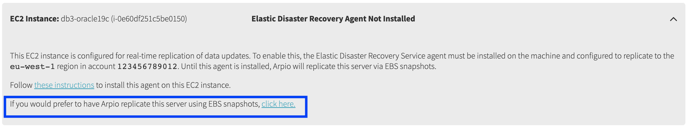 Following this link will produce a new dialogue prompting you to update your preference for the server in question. Click Use Snapshots to confirm this choice.
Following this link will produce a new dialogue prompting you to update your preference for the server in question. Click Use Snapshots to confirm this choice.
.png?width=688&name=image%20(3).png)
Set up real-time replication on secure networks
Real-time replication can also be enabled for secure networks. To set up real-time replication on secure networks:
- Set up a secure connection between your source environment that the EC2 instance lives in and your recovery environment that Arpio will use to launch instances. A secure connection can be established with a VPC peering connection, transit gateway, or VPN.
- Create a VPC endpoint in your recovery environment for Elastic Disaster Recovery, EC2, EC2 Messages, and an interface gateway for S3. Note: The security group you use when setting up the DRS endpoint must allow inbound HTTPS (443) connections.
- Change the default replication settings in the Elastic Disaster Recovery console for “Use private IP for data replication” set to “Yes” and ‘Create public IP’ set to “No’’.