Deploy Access with AWS StackSets
Use CloudFormation StackSets to deploy Arpio access across multiple AWS accounts from a central management account. StackSets simplify access management by allowing you to deploy and update Arpio permissions across your entire organization from a single location.
For a scaled approach: the docs here describe how to automate StackSets deployment using the Arpio API and AWS CloudFormation CLI.
Jump to:
- Overview
- Prerequisites
- Step 1: Create IAM Roles
- Step 2: Create StackSets
- Step 3: Deploy Stack Instances
- Scenario: Migrating from CloudFormation Templates
- Adding Additional Applications
Overview
AWS CloudFormation StackSets extend CloudFormation functionality by enabling you to create, update, or delete stacks across multiple accounts and regions with a single operation. For Arpio, this means you can manage access permissions for all your applications from your AWS management account.
Benefits of using StackSets:
- Centralized management: Deploy and update Arpio access from a single management account
- Simplified updates: When Arpio releases permission updates, apply them once to update all accounts
- Reusable across applications: A single StackSet pair can serve your entire organization
- Consistent permissions: Ensure all accounts have identical Arpio access configurations
StackSets Architecture Components:
|
Component |
Quantity |
Scope |
Notes |
|
Administration Role |
1 |
Management account |
One-time setup, enables StackSet operations |
|
Execution Role |
1 per account |
Each target account |
Allows StackSets to deploy resources |
|
StackSets |
1 pair (minimum) |
Management account |
Primary + Recovery; reusable for all apps |
|
Stack Instances |
1 per account/region |
Target accounts |
Deploys actual Arpio access roles |
Prerequisites
Before you begin, ensure you have:
- AWS Management Account: An AWS account designated as your management account for StackSet operations
- Target AWS Accounts: The source (primary) and recovery AWS accounts for your Arpio application
- AWS CLI or CloudShell: Access to run AWS CLI commands in each account
- IAM Permissions: Administrator access or permissions to create IAM roles and CloudFormation StackSets
ℹ️ Note: Best practice is for your management account to be a dedicated account (separate from your primary or recovery workload accounts).
Getting Started
To deploy Arpio access with StackSets, start by creating a new application in Arpio:
- Log in to your Arpio account
- Click Create New Application
- Enter your application name, source account/region, and recovery account/region
- Set your Recovery Point Objective (RPO)
- Click Continue
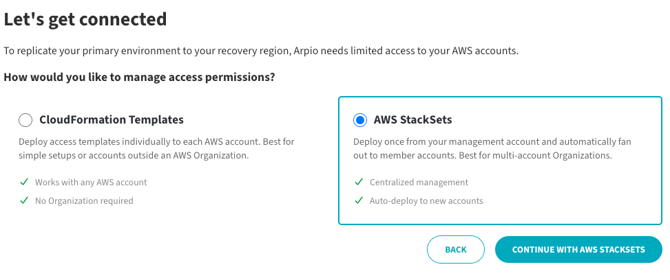
On the next screen, you will see “AWS StackSets” as an option to manage Arpio’s access permissions. Select “AWS StackSets” and Click the “CONTINUE WITH AWS STACKSETS” button.
On the next screen, you will see the StackSets deployment instructions. The page is organized into three main steps:
- Step 1: Set Up IAM Roles (Administration Role + Execution Roles)
- Step 2: Create StackSets (Primary Access + Recovery Access)
- Step 3: Deploy Stack Instances to your target accounts
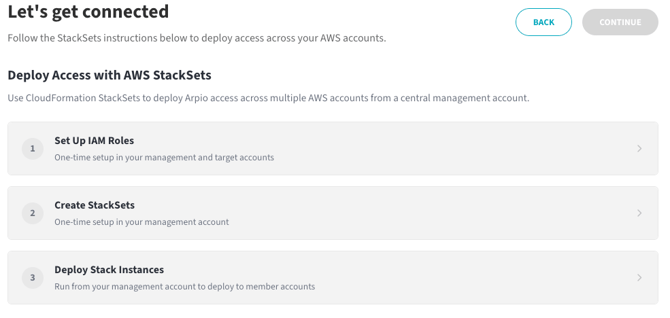
Figure 2: Deploy Access with AWS StackSets - Overview
Step 1: Create IAM Roles
StackSets require two IAM roles to operate: an Administration Role in your management account, and an Execution Role in each target account.
1a. Create Administration Role
The Administration Role is deployed once in your management account. It allows CloudFormation to assume roles in your target accounts.
- Enter your Management Account ID in the input field. (This can be found by going to AWS Organizations in the AWS console from a member account.)
- Open AWS CloudShell (or AWS CLI) using an Administrator role in your management account
- Click Copy or Download to get the Administration Role command
- Paste and run the command in CloudShell
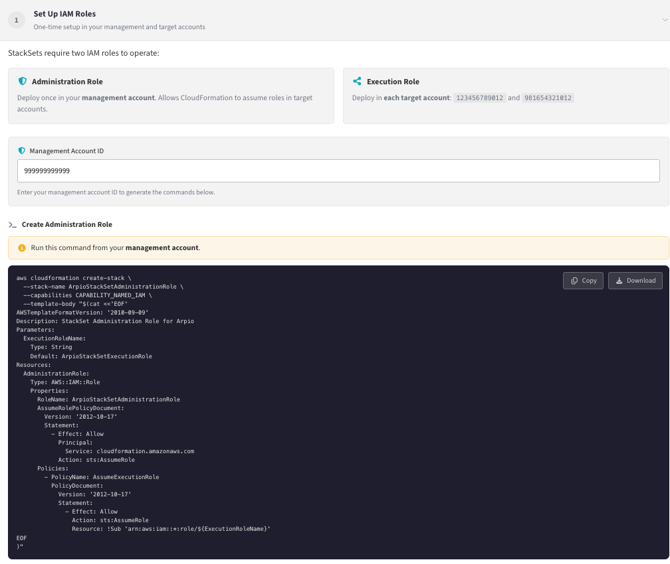
The command creates a CloudFormation stack named ArpioStackSetAdministrationRole. Wait for the stack creation to complete before proceeding.
Expected output:
{ "StackId": "arn:aws:cloudformation:us-east-1:YOUR-ACCOUNT:stack/ArpioStackSetAdministrationRole/..."}
1b. Create Execution Roles
The Execution Role must be deployed in each target account (your primary account and recovery account). This role allows the StackSet to deploy resources in those accounts.
- Open AWS CloudShell in your primary account
- Copy the Execution Role command from the Arpio UI
- Run the command
- Repeat for your recovery account
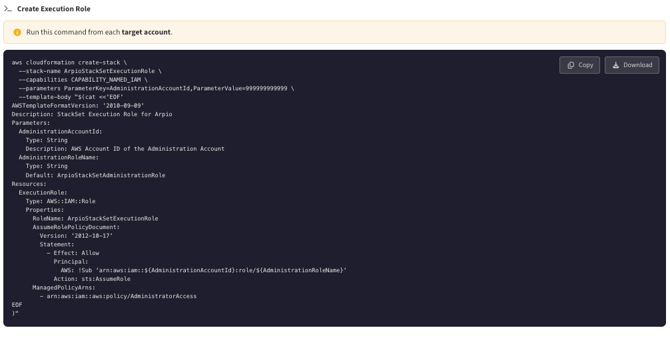
Figure 3: Create Execution Role command
💡 Tip: IAM roles are global resources. You only need to create the Execution Role once per account, regardless of which region you run the command in.
Step 2: Create StackSets
Create two StackSets in your management account: one for Primary Access and one for Recovery Access.
- Enter names for your StackSets in the input fields (e.g., ArpioPrimaryAccess and ArpioRecoveryAccess)
- Open AWS CloudShell in your management account
- Copy and run the Primary Access StackSet command
- Copy and run the Recovery Access StackSet command
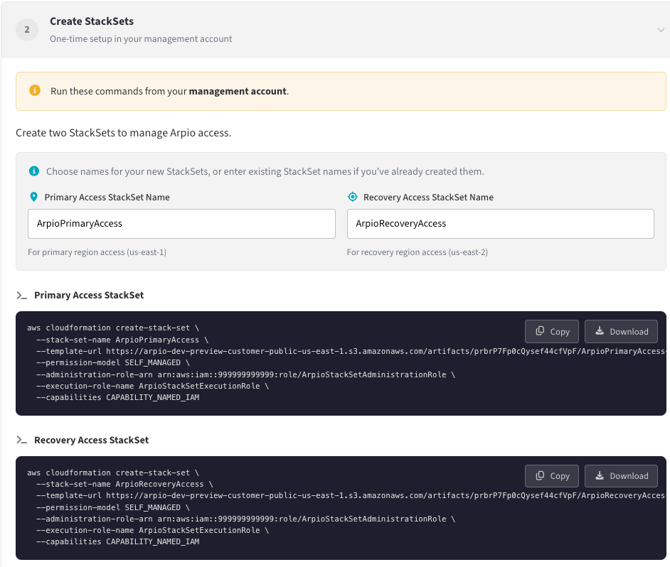
Figure 4: Create StackSets - Primary and Recovery Access
💡 Tip: If you already have StackSets from a previous application setup, you can skip this step and enter the existing StackSet names in the input fields.
Step 3: Deploy Stack Instances
Stack Instances deploy the actual Arpio access roles to your target accounts. Run these commands from your management account.
- Copy and run the Primary Access Stack Instance command
- Copy and run the Recovery Access Stack Instance command
- Wait 1-3 minutes for the Stack Instances to deploy
- Click Test Access to verify the deployment
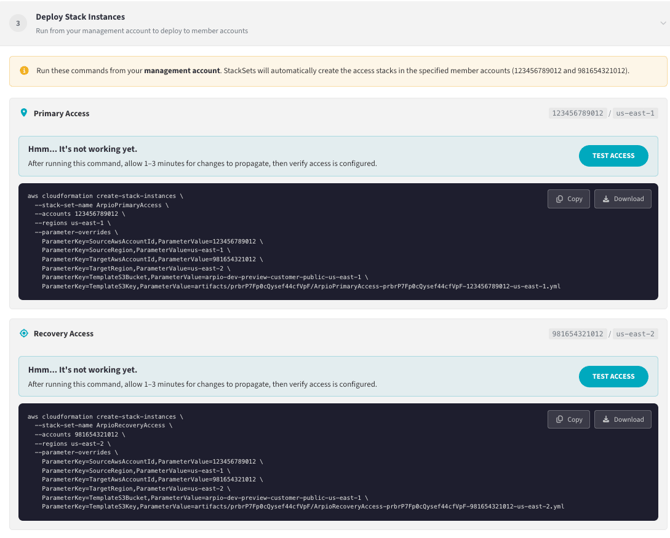
Figure 5: Deploy Stack Instances - Primary Access and Recovery Access
When validation succeeds, you will see green checkmarks next to both Primary Access and Recovery Access. The Continue button will become enabled.
Click Continue to complete the application setup and proceed to resource selection.
Scenario: Migrating from CloudFormation Templates
If your AWS accounts already have Arpio access deployed via individual CloudFormation templates, you will see a warning message at Step 3.
The warning indicates:
⚠️ An existing Arpio CloudFormation stack (stack-name) exists in this account.Deploying via StackSets may fail if IAM roles conflict. Consider usingCloudFormation for this app, or remove the existing stack first.
You have two options:
Option 1: Continue using CloudFormation templates for this application
If you prefer to keep your existing setup, click Back and choose the CloudFormation deployment method instead of StackSets.
Option 2: Migrate to StackSets
To migrate to StackSets, you must first remove the existing CloudFormation stacks:
- Open the AWS CloudFormation console in the affected account
- Locate the existing Arpio access stack (name shown in the warning)
- Delete the stack
- Wait for deletion to complete
- Repeat for any other accounts with existing stacks
- Return to Arpio and run the Stack Instance commands
⚠️ Warning: Deleting the CloudFormation stack will temporarily remove Arpio's access to the account. Complete the Stack Instance deployment promptly to restore access.
Adding Additional Applications
One of the key benefits of StackSets is reusability. When you create additional Arpio applications, you can reuse your existing StackSets.
Same accounts, different regions:
- Skip Step 1 (IAM roles already exist in those accounts)
- Skip Step 2 (enter your existing StackSet names)
- Run Step 3 only (deploy new Stack Instances for the new regions)
Different accounts:
- Run Step 1b only (create Execution Roles in the new accounts)
- Skip Step 2 (enter your existing StackSet names)
- Run Step 3 (deploy Stack Instances for the new account/region combinations)
💡 Tip: A single StackSet pair can serve your entire organization. You only need to create additional StackSets if you prefer to organize them separately for different teams or environments.
Troubleshooting
The Arpio UI includes expandable troubleshooting sections for each step. If you encounter issues:
Stack already exists error:
If you see an error that a stack already exists, you may need to delete the existing CloudFormation stack before running the command again. Check the CloudFormation console in the appropriate account.
Access validation fails:
Wait 1-3 minutes after deploying Stack Instances, then click Test Access again. If it continues to fail, verify that all Stack Instance deployments completed successfully in the CloudFormation console.
Permission denied errors:
Ensure you have administrator access or appropriate IAM permissions to create roles and StackSets. The Execution Role requires the account ID of your management account—verify this value is correct.
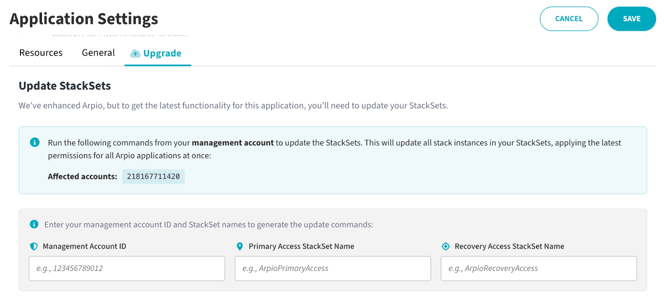
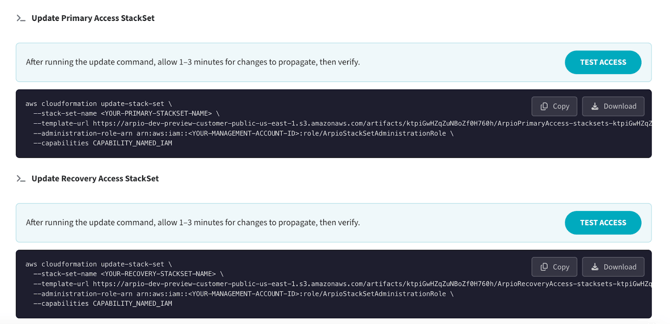
Updating Stack Instances
Arpio periodically updates our permissions to introduce new capabilities to our automation. When that happens, a new set of CloudFormation templates are generated.
Template updates can be issued via CloudFormation in your management account using the following command:
aws cloudformation update-stack-set \
--stack-set-name <YOUR-PRIMARY-STACKSET-NAME> \
--template-url <arpio-template-url> \
--administration-role-arn arn:aws:iam::<YOUR-MANAGEMENT-ACCOUNT-ID>:role/ArpioStackSetAdministrationRole \
--capabilities CAPABILITY_NAMED_IAM
This command will need to be run once for each StackSet (primary and recovery). This will update the templates for all of the stack instances managed by each. The S3 template URL referenced in the command will not change.
In the Arpio console, you’ll be prompted to update your StackSets in the Application Settings “Upgrade” tab when a new template version is available. The above command will be automatically generated for the user to apply to their StackSets. Regardless of which application you access this command from, it will only need to be run once per StackSet to update all Arpio applications.
…
Summary
Deploying Arpio access with StackSets provides centralized management and simplified updates across your organization. The key steps are:
- Create IAM Roles: Administration Role in management account, Execution Role in each target account
- Create StackSets: Primary Access and Recovery Access StackSets in management account
- Deploy Stack Instances: Deploy to each account/region combination, then verify with Test Access
Once configured, your StackSets can be reused for all future Arpio applications, requiring only new Stack Instances for additional account/region combinations.